Operating system: Windows, Android, macOS
Group of programs: Business automation
Security system
- Copyright protects the unique methods of business automation that are used in our programs.

Copyright - We are a verified software publisher. This is displayed in the operating system when running our programs and demo-versions.

Verified publisher - We work with organizations around the world from small businesses to large ones. Our company is included in the international register of companies and has an electronic trust mark.

Sign of trust
Quick transition.
What do you want to do now?
If you want to get acquainted with the program, the fastest way is to first watch the full video, and then download the free demo version and work with it yourself. If necessary, request a presentation from technical support or read the instructions.

Contact us here
During business hours we usually respond within 1 minute
How to buy the program?
View a screenshot of the program
Watch a video about the program
Download demo version
Compare configurations of the program
Calculate the cost of software
Calculate the cost of the cloud if you need a cloud server
Who is the developer?
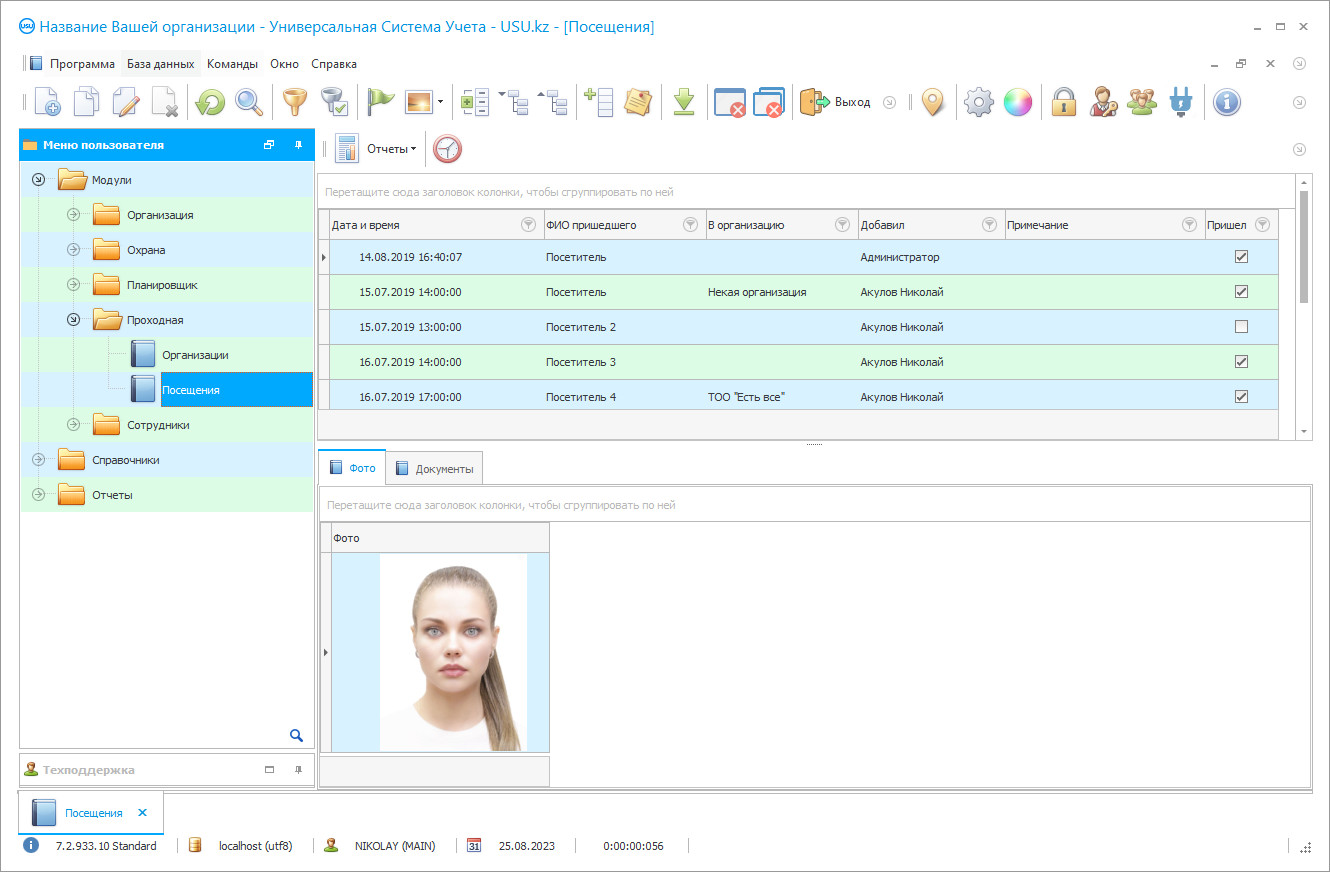
Program screenshot
A screenshot is a photo of the software running. From it you can immediately understand what a CRM system looks like. We have implemented a window interface with support for UX/UI design. This means that the user interface is based on years of user experience. Each action is located exactly where it is most convenient to perform it. Thanks to such a competent approach, your work productivity will be maximum. Click on the small image to open the screenshot in full size.
If you buy a USU CRM system with a configuration of at least “Standard”, you will have a choice of designs from more than fifty templates. Each user of the software will have the opportunity to choose the design of the program to suit their taste. Every day of work should bring joy!
The security system in our information program is thought out logically and rationally. The tool is launched from a shortcut on the desktop. Next, the login window appears. Each user in the security system works under a separate login, which is protected by his password. Also, each employee can have individual access rights included in the area of his authority. Separate rights configured for managers and ordinary employees of organizations. Let's go under the main role, that is, the main one, to see all the functionality. Maintaining a security system using this program is very easy to carry out. After all, it consists of only three main blocks: modules, reference books, and reports. To get started in the system, you should fill out the reference books once to automate all cardinal and financial estimations. If your institution works with money from various countries, they are recorded in the appropriate section. Your cash till and non-cash invoices are pointed at the cash till. In the division of the financial article, the expenses and profits reason is filled in, in the sources of information - a list of information you know about your company. The discount division allows creating special service prices for specific consumers. Services are a catalog of the services you provide, with an indication of their cost. For the convenience of maintaining the security system, your list can be divided into the necessary categories. With the help of the reference book, the system itself carry out all the necessary calculations. All the fundamental work in the security agency system takes place in the modules block. To register a new application, use the orders tab. To tag a new entry, right-click in a space in the table and select add. So the system automatically sets the current one. If necessary, this parameter set manually. Next, you should indicate the counterparties. Simultaneously, the program itself guides us to the consumer base. We got to new tab clients. If the counterparty is in the data bank, you just need to choose it. For a quick search, just enter the first letter of the name or phone number. If the client is new, we easily register him, indicating the contact information, address, availability of a discount, information about the contract. Having selected a counterparty, we automatically return to the previous order registration window. Now you need to select the service provided from the catalog you have already filled out. It remains only to enter the required calculation parameter. These are, for example, the approximate protection times and the number of visits. If necessary, you can fill in the note ‘order registered’. In each parameter database, you can perform a quick search or group or order by specific criteria. For example, current month services. All funds obtained from the customer are recorded in the defrayal field. The instrument calculates the total amount to be paid automatically. The information mechanism monitors the debts and prepayments of clients. In the money tab, you can audit any cash flows. In the security system, each entry is recorded with the exact date, financial item, and amount. In the reports block, financial and management statistical necessary accounting is generated. A detailed accounting of the movement of funds provides an analysis of all financial items, changes in expenses, and the previous month's income. Sources of information allow you to analyze your marketing activities and spending on PR justification. The service compendium provides financial and quantitative statistics on the selected services provided by the security firm. Please notice that this set is basic. If you need to take into account something in addition, we easily add new features to the security program.
Who is the developer?
Akulov Nikolay
Expert and chief programmer who participated in the design and development of this software.
2024-11-22
Video of security system
This video is in Russian. We have not yet managed to make videos in other languages.
Maintaining an information instrument security system has a single client base of the organization, which speeds up the notification process in the event of some changes, monetary control, and quick search. When conducting security with the help of our information tool, it is possible to divide the agency's clients into the necessary categories. The database automatically saves all phone numbers, addresses, and details, which greatly speeds up the workflow. Any number of services can be registered in our system. Convenient search by service name, category, clients also optimizes the entire workflow and workload of the organization's employees. Using the information conducting security companies system, payment can be accepted both in cash, that is, in money, and by non-cash payment, using cards and transfers. Here you can also keep track of the account of prepayment and debt. With the help of our information tool, you can analyze the income and expenses of your security company without unnecessary red tape and headaches. When checking the reports of the enterprise, it is possible to illustrate the data with graphs, charts, and visual tables.
Download demo version
When starting the program, you can select the language.
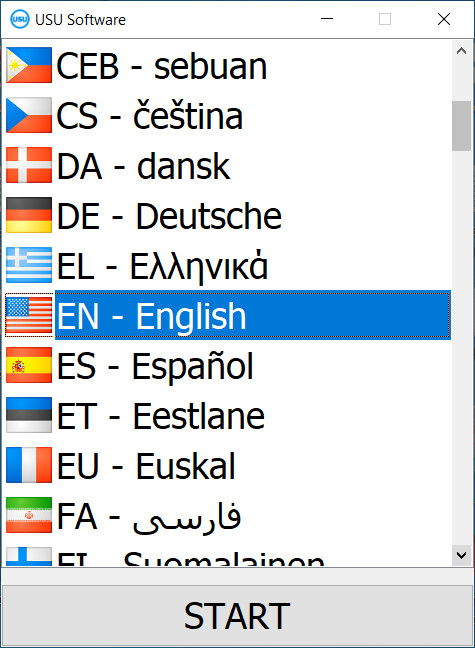
You can download the demo version for free. And work in the program for two weeks. Some information has already been included there for clarity.
Who is the translator?
Khoilo Roman
Chief programmer who took part in the translation of this software into different languages.
USU Software offers derivation analysis of advertising effectiveness and other costs using your database. Conducting security involves working with counterparties, and thus, communicating with them by calls and messages. To simplify this task, you can use the function of automatic calls to the customer base. Also, you receive a notification about the status of the order, debts, deadlines, and departures, which minimizes the impact of the human factor on the profit and the prestige of the organization. With the help of the notification properties of the working tool, you will not forget to make a payment or, on the contrary, demand debts from clients. One of the security functions can automatically translate your audio recordings into text messages. A security information system can also do much more!
Order a security system
To buy the program, just call or write to us. Our specialists will agree with you on the appropriate software configuration, prepare a contract and an invoice for payment.
How to buy the program?
Send details for the contract
We enter into an agreement with each client. The contract is your guarantee that you will receive exactly what you require. Therefore, first you need to send us the details of a legal entity or individual. This usually takes no more than 5 minutes

Make an advance payment
After sending you scanned copies of the contract and invoice for payment, an advance payment is required. Please note that before installing the CRM system, it is enough to pay not the full amount, but only a part. Various payment methods are supported. Approximately 15 minutes

The program will be installed
After this, a specific installation date and time will be agreed upon with you. This usually happens on the same or the next day after the paperwork is completed. Immediately after installing the CRM system, you can ask for training for your employee. If the program is purchased for 1 user, it will take no more than 1 hour
Enjoy the result
Enjoy the result endlessly :) What is especially pleasing is not only the quality with which the software has been developed to automate everyday work, but also the lack of dependency in the form of a monthly subscription fee. After all, you will only pay once for the program.
Buy a ready-made program
Also you can order custom software development
If you have special software requirements, order custom development. Then you won’t have to adapt to the program, but the program will be adjusted to your business processes!