Operating system: Windows, Android, macOS
Group of programs: Business automation
Management of visits
- Copyright protects the unique methods of business automation that are used in our programs.

Copyright - We are a verified software publisher. This is displayed in the operating system when running our programs and demo-versions.

Verified publisher - We work with organizations around the world from small businesses to large ones. Our company is included in the international register of companies and has an electronic trust mark.

Sign of trust
Quick transition.
What do you want to do now?
If you want to get acquainted with the program, the fastest way is to first watch the full video, and then download the free demo version and work with it yourself. If necessary, request a presentation from technical support or read the instructions.

Contact us here
During business hours we usually respond within 1 minute
How to buy the program?
View a screenshot of the program
Watch a video about the program
Download demo version
Compare configurations of the program
Calculate the cost of software
Calculate the cost of the cloud if you need a cloud server
Who is the developer?
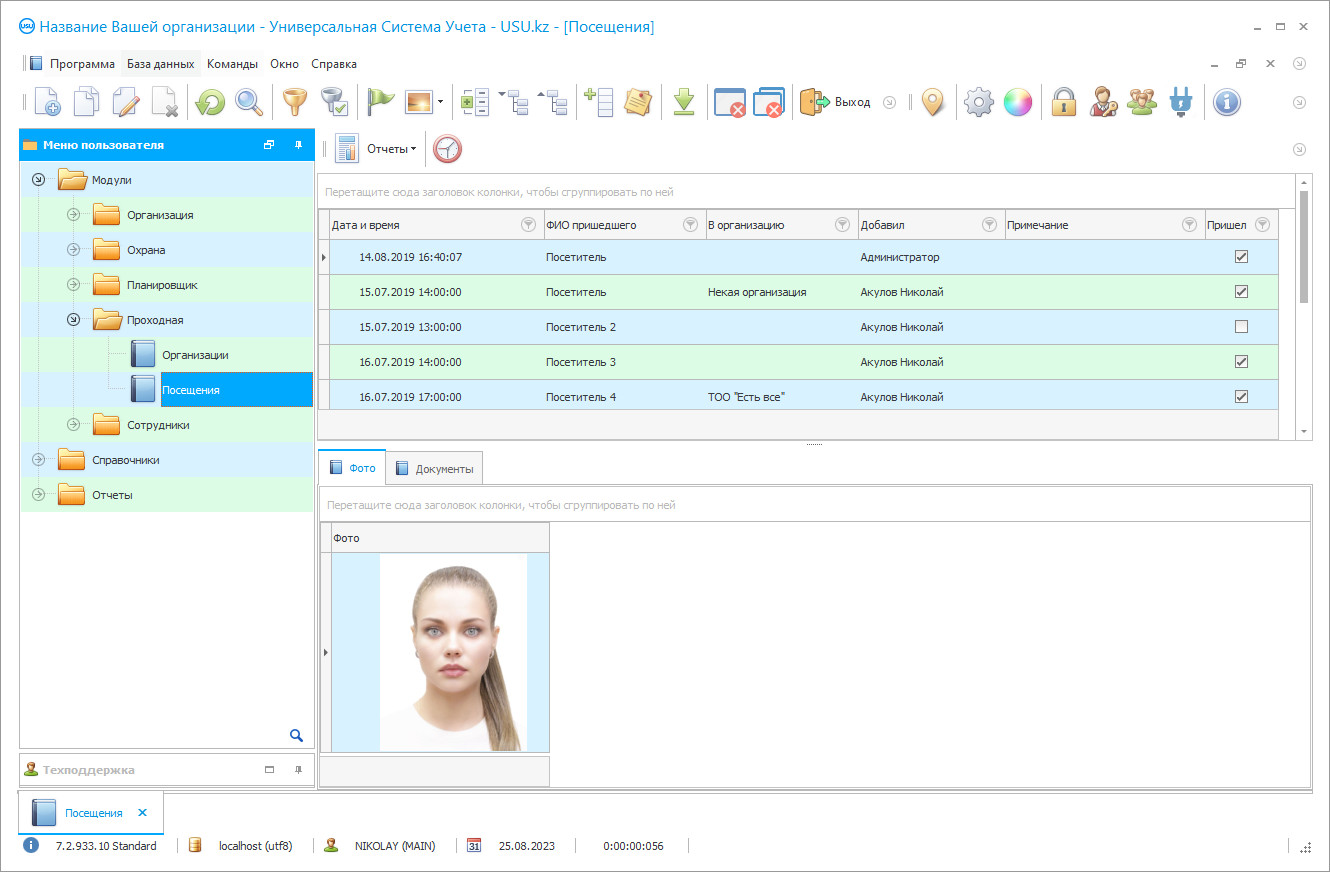
Program screenshot
A screenshot is a photo of the software running. From it you can immediately understand what a CRM system looks like. We have implemented a window interface with support for UX/UI design. This means that the user interface is based on years of user experience. Each action is located exactly where it is most convenient to perform it. Thanks to such a competent approach, your work productivity will be maximum. Click on the small image to open the screenshot in full size.
If you buy a USU CRM system with a configuration of at least “Standard”, you will have a choice of designs from more than fifty templates. Each user of the software will have the opportunity to choose the design of the program to suit their taste. Every day of work should bring joy!
Visits are managed in almost any more or less large company, not to mention the business center, where the offices of many organizations are located. The task of such management involves the need to record the fact of a visit, identify a visitor, record his personal data, control the duration of the presence of a given person at a protected facility. All these actions can be carried out, as they say, in an old-fashioned way, that is, using paper logbooks, handwriting passes, and so on. Despite its laboriousness and dubious efficiency, this method is still widely used in many organizations. Its doubtfulness is due, first of all, to the fact that it is extremely difficult then to look for the necessary information in these records. And there is no need to talk about any samples by periods, by companies, etc., analysis of visits, and so on. In modern conditions, a much more effective tool is a computerized visit management system, which provides automation of basic procedures, accurate accounting, and storage of information in electronic databases. Accordingly, the security of the organization is better ensured.
Who is the developer?
Akulov Nikolay
Expert and chief programmer who participated in the design and development of this software.
2024-11-22
Video of management of visits
This video is in Russian. We have not yet managed to make videos in other languages.
USU Software offers its own unique visit management program, developed at a high professional level and meeting modern business standards. Registration of visitors is carried out promptly and professionally. Employees of the company, or of the tenant companies, if we are talking about the entrance of the business center can order a pass for important partners who must arrive at the meeting. The reader automatically reads your passport or ID data with no need to manually fill out a log that records visits and uploads it directly to the accounting spreadsheets. Thanks to the camera built into the control program, a badge with a guest's photo can be printed directly at the entrance. If necessary, government databases can be integrated into the program. Identity card or passport data, including photos, should be automatically checked against the list of wanted persons, criminals, etc. in order to provide additional protection. Electronic turnstiles are remotely controlled and equipped with a passage counter that allows you to accurately determine the number of people passing through the point of entry into the building during the day.
Download demo version
When starting the program, you can select the language.
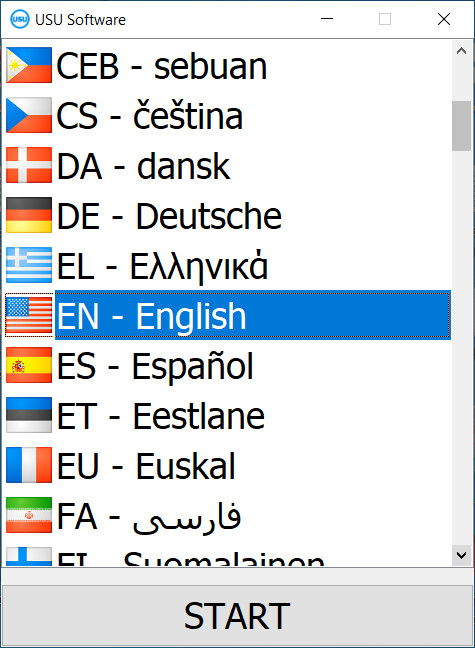
You can download the demo version for free. And work in the program for two weeks. Some information has already been included there for clarity.
Who is the translator?
Khoilo Roman
Chief programmer who took part in the translation of this software into different languages.
Management accounting of visits in this program is carried out using an electronic database that stores document data and a complete history of visits of each guest, including the date, time, receiving unit, length of stay, etc. The statistical information is conveniently structured. The built-in filter system allows you to quickly form samples according to specified parameters, explore information arrays using statistical analysis methods, create analytical reports on the dynamics of visits, improve the level of management of visits, and so on. Thanks to accurate accounting, the security service knows exactly how many people are in the building at any given time. This is especially important in case of emergency situations such as fires, smoke, threats of terrorist attacks, and so on. Thanks to the professional visit management provided by the USU Software, the company must be confident in the loyalty and reliability of its visitors, the safety of its employees, and material resources.
Order a management of visits
To buy the program, just call or write to us. Our specialists will agree with you on the appropriate software configuration, prepare a contract and an invoice for payment.
How to buy the program?
Send details for the contract
We enter into an agreement with each client. The contract is your guarantee that you will receive exactly what you require. Therefore, first you need to send us the details of a legal entity or individual. This usually takes no more than 5 minutes

Make an advance payment
After sending you scanned copies of the contract and invoice for payment, an advance payment is required. Please note that before installing the CRM system, it is enough to pay not the full amount, but only a part. Various payment methods are supported. Approximately 15 minutes

The program will be installed
After this, a specific installation date and time will be agreed upon with you. This usually happens on the same or the next day after the paperwork is completed. Immediately after installing the CRM system, you can ask for training for your employee. If the program is purchased for 1 user, it will take no more than 1 hour
Enjoy the result
Enjoy the result endlessly :) What is especially pleasing is not only the quality with which the software has been developed to automate everyday work, but also the lack of dependency in the form of a monthly subscription fee. After all, you will only pay once for the program.
Buy a ready-made program
Also you can order custom software development
If you have special software requirements, order custom development. Then you won’t have to adapt to the program, but the program will be adjusted to your business processes!
Management of visits
This visit management system is intended for use by the security service of a business center, a large company, etc. at checkpoints and other points of entry into protected buildings. This visit management program is developed at a high professional level and meets modern quality standards. System settings are made for a specific customer, taking into account his requirements, features of protected buildings, and internal accounting rules. When using this program, strict adherence to the established checkpoint regime is ensured. Electronic gates with remote control and passage counters ensure accurate counting of the number of people passing through the entry point during the day. In the event of emergency events, such as fires, explosions, and so on, the security service knows exactly how many people are in the building, and is able to take adequate measures to get them out and rescue them, and generally manage the situation. Employees of the company can order passes in advance for important visitors arriving at a business meeting through the program. A camera can be integrated into the system for printing a badge with a photo. Information from the passport and identity card is read by a special device and loaded into digital accounting tables.
The visitor base saves passport data and a complete history of visits, including the date, time of the visit, the receiving unit, duration of stay, and so on. Thanks to a well-thought-out filter system, statistics can be used to create samples, prepare analytical reports on the dynamics of visits, the process using methods of mathematical analysis, etc. Visits management also applies to the vehicles of visitors, which are recorded in a separate database. The system provides for the possibility of creating and replenishing the so-called blacklist of people who are prohibited from entering the protected building for various reasons. If necessary, mobile applications can be activated for employees and customers of the company, providing an opportunity for closer contact with clients.