Operating system: Windows, Android, macOS
Group of programs: Business automation
Protection control on facility
- Copyright protects the unique methods of business automation that are used in our programs.

Copyright - We are a verified software publisher. This is displayed in the operating system when running our programs and demo-versions.

Verified publisher - We work with organizations around the world from small businesses to large ones. Our company is included in the international register of companies and has an electronic trust mark.

Sign of trust
Quick transition.
What do you want to do now?
If you want to get acquainted with the program, the fastest way is to first watch the full video, and then download the free demo version and work with it yourself. If necessary, request a presentation from technical support or read the instructions.

Contact us here
During business hours we usually respond within 1 minute
How to buy the program?
View a screenshot of the program
Watch a video about the program
Download demo version
Compare configurations of the program
Calculate the cost of software
Calculate the cost of the cloud if you need a cloud server
Who is the developer?
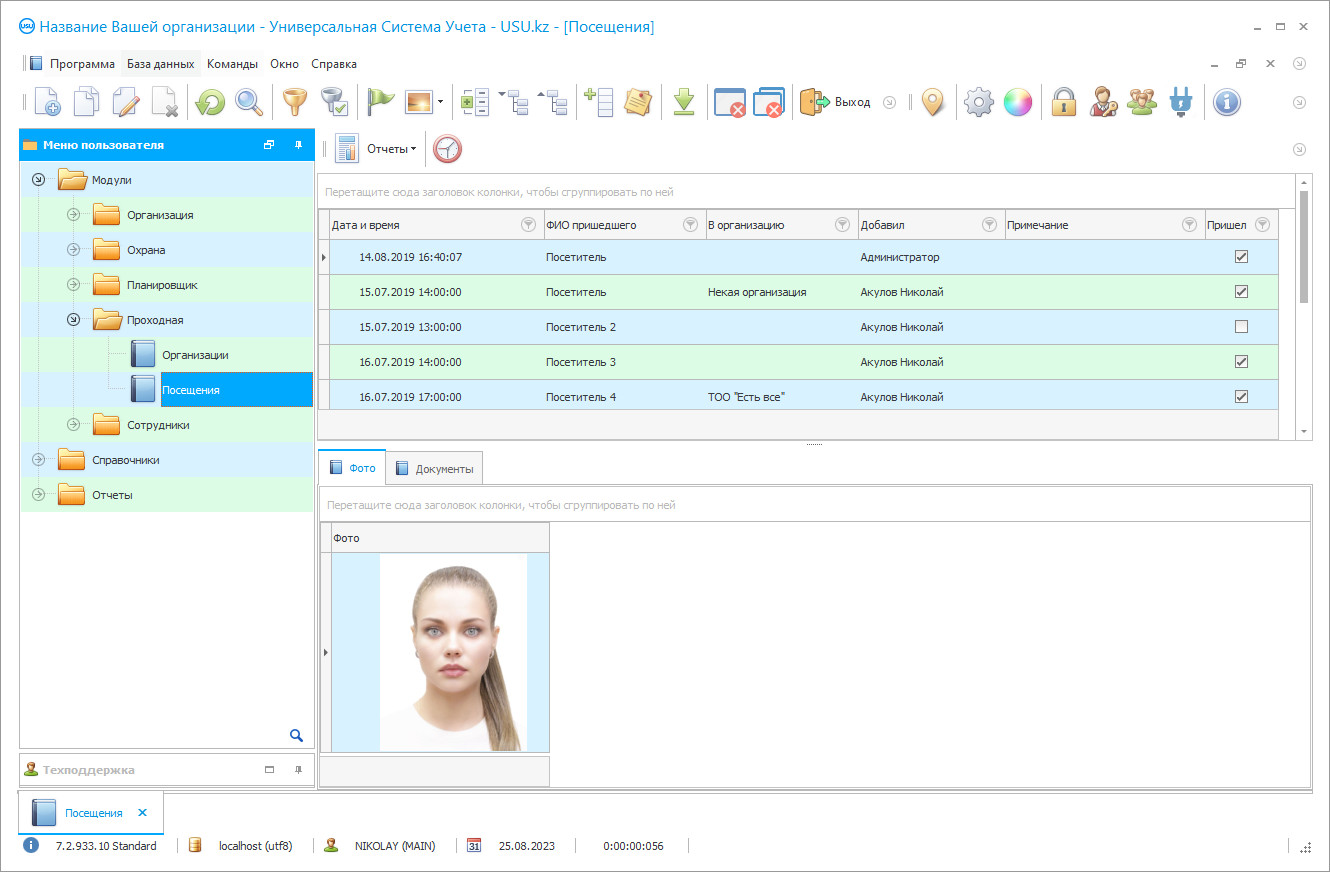
Program screenshot
A screenshot is a photo of the software running. From it you can immediately understand what a CRM system looks like. We have implemented a window interface with support for UX/UI design. This means that the user interface is based on years of user experience. Each action is located exactly where it is most convenient to perform it. Thanks to such a competent approach, your work productivity will be maximum. Click on the small image to open the screenshot in full size.
If you buy a USU CRM system with a configuration of at least “Standard”, you will have a choice of designs from more than fifty templates. Each user of the software will have the opportunity to choose the design of the program to suit their taste. Every day of work should bring joy!
Protection control at the facility today is carried out not only through visual control, perimeter bypasses, etc., but also using a wide variety of technical means. For example, protection personnel can be provided with special communicators-readers of proximity tags. The indicated marks are installed along the route of bypassing the territory under protection. The corresponding software registers the passed contact marks during the patrol, as well as records all events noted along the way (unlocked door, broken glass, broken fence, etc.). All these data are stored in the system memory and are available for viewing. Of course, a modern computer system used by the protection service must necessarily use various sensors, cameras, electronic locks, fire alarms, etc. Otherwise, the fulfillment of the main protection tasks (ensuring order on the territory, observing the control people and vehicles regime, periodically patrolling the territory, preventing theft, etc.) not sufficiently effective.
Hence, the control of protection at the facility in modern conditions is practically impossible without the use of IT technologies. The USU Software system offers its own unique computer development that meets modern programming standards and meets the highest protection control at the facility requirements. The USU Software ensures the streamlining of all business processes, transparency, and timeliness of accounting procedures, automation of analysis, planning tasks, etc. The product can work, if necessary, in several languages simultaneously (just download the appropriate language packs). The interface is simple and straightforward to learn, does not require much effort and time. The modular structure of the program allows customizing and modifying various subsystems, taking into account the characteristics of the customer and the protected enterprise facility. There are separate monitoring of the work of the checkpoint modules, shift work of employees, the serviceability of protection alarms, accounting and recording of each object authorized persons, etc. By the way, the number of facility objects under protection can be as large as you like. The program allows providing their control all at the same time. In the process of monitoring protection at the facility, integration into the program of various technical devices (motion sensors, points of contactless tags, video surveillance cameras, humidity, and temperature control sensors, fire alarms, electronic locks and turnstiles, video recorders, and navigators, etc.) is provided. Automation of the checkpoint allows clearly recording the time of arrival and departure of each employee of the facility, generate reports on the number of delays, absenteeism, overtime to each employee individually, and a summary report to the company as a whole.
Who is the developer?
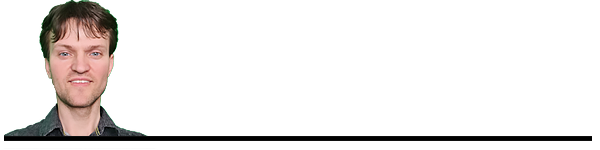
Akulov Nikolay
Expert and chief programmer who participated in the design and development of this software.
2024-11-22
Video of protection control on facility
This video is in Russian. We have not yet managed to make videos in other languages.
The heads of various departments of the protection service are provided with management reports, customizable according to their wishes and allowing them to track the location of any employee, the frequency and timeliness of the patrol route, promptly receive messages about any emergency situations and incidents, carry out general control of the situation, etc. areas of the territory, allowing you to accurately localize the event, find a person on the territory. The proposed program ensures the maintenance of highly effective protection of any complex facility.
The specialized computer program of the USU Software is designed to effectively solve the tasks of monitoring security at the facility.
Download demo version
When starting the program, you can select the language.
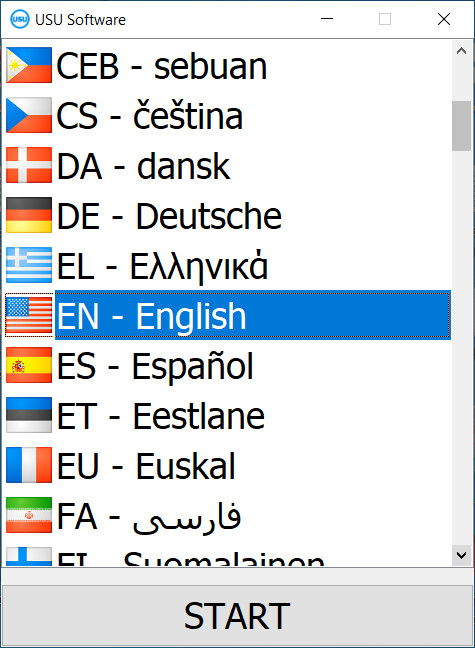
You can download the demo version for free. And work in the program for two weeks. Some information has already been included there for clarity.
Who is the translator?
Khoilo Roman
Chief programmer who took part in the translation of this software into different languages.
USU Software carries out the ordering and automation of all work processes within the protection of the enterprise. The offered IT solution meets the highest modern requirements and professional standards.
USU Software provides protection and control over an unlimited number of objects. The protection management system is configured taking into account the characteristics of the customer and the protected facility organizations. The program can be used for production, trade, facility, service, etc. enterprise, business center, security facility, government agency, etc. Information arising in the process of guarding enterprises under the control of the security service is stored in a centralized database. The system can be integrated with various technical devices (sensors, cameras, electronic locks, etc.) used to improve the efficiency of protection. Each signal generated by the devices is recorded by the program and automatically transmitted to the appropriate employee to solve the facility work problem. For each protected facility, a list of authorized persons related to the control is formed, containing personal and contact information. Formation of security service schedules changes, duty schedules, each facility general work plans is automated. The counterparty database is created and updated centrally, contains all contact information. The system provides effective access control, fixing the exact time of arrival and departure of each employee, provides collection, processing, and analysis of data on-site visits by unauthorized persons. One-time and permanent passes with the attachment of a photograph of the person who received a pass to the protected area are printed on the spot thanks to the built-in web camera.
Order a protection control on facility
To buy the program, just call or write to us. Our specialists will agree with you on the appropriate software configuration, prepare a contract and an invoice for payment.
How to buy the program?
Send details for the contract
We enter into an agreement with each client. The contract is your guarantee that you will receive exactly what you require. Therefore, first you need to send us the details of a legal entity or individual. This usually takes no more than 5 minutes

Make an advance payment
After sending you scanned copies of the contract and invoice for payment, an advance payment is required. Please note that before installing the CRM system, it is enough to pay not the full amount, but only a part. Various payment methods are supported. Approximately 15 minutes

The program will be installed
After this, a specific installation date and time will be agreed upon with you. This usually happens on the same or the next day after the paperwork is completed. Immediately after installing the CRM system, you can ask for training for your employee. If the program is purchased for 1 user, it will take no more than 1 hour
Enjoy the result
Enjoy the result endlessly :) What is especially pleasing is not only the quality with which the software has been developed to automate everyday work, but also the lack of dependency in the form of a monthly subscription fee. After all, you will only pay once for the program.
Buy a ready-made program
Also you can order custom software development
If you have special software requirements, order custom development. Then you won’t have to adapt to the program, but the program will be adjusted to your business processes!
Protection control on facility
The USU Software records not only the time and duration of the visit but also the visitor's personality, the purpose of his visit. By an additional order, the program activates customers and employees of the company's mobile applications. To control and ensure the protection of valuable information, the parameters of regular database backups to secure storage are configured.